
Your router is the most trusted device in your network. It sits quietly between every device you own and the internet, routing traffic, managing connections, and rarely drawing attention. Unlike laptops or smartphones, it is almost never monitored, rarely updated, and often forgotten entirely.
That invisibility is precisely what makes it dangerous.
Cheap router security risks are no longer theoretical. Low-cost networking devices have become one of the most exploited entry points in modern cybersecurity. From botnets that can take down major internet infrastructure to silent surveillance mechanisms capable of intercepting traffic, compromised routers operate as hidden control points inside homes, businesses, and even critical infrastructure.
The problem is not just technical. It is structural. Manufacturers competing on price often sacrifice firmware quality, long-term support, and security testing. Devices ship with weak default credentials, outdated software, and exposed services. Many are never patched. Some are never designed to be.
The result is a growing class of devices that function less like secure infrastructure and more like Trojan horses embedded directly into your network.
This article examines how cheap routers create systemic risk, how attackers exploit them, and what you can do to reduce exposure without overspending.
Why Cheap Routers Create Outsized Security Risks
The economics of insecure hardware
The economics of consumer networking hardware incentivize insecurity.
Low-cost routers are built to win on price, not resilience. Margins are thin, competition is intense, and product cycles are short. Security engineering, unlike hardware components, does not produce visible marketing value. As a result, it is often minimized.
This manifests in several predictable ways:
- Limited investment in secure firmware development
- Minimal or nonexistent penetration testing
- Short update lifecycles, sometimes ending within a few years
- Lack of dedicated security response teams
Unlike enterprise networking vendors, many low-cost manufacturers do not maintain long-term patch pipelines. Once a product is shipped, security becomes a cost center rather than a priority.
This creates a dangerous asymmetry. Attackers continuously develop new exploits, while devices in the field remain static and increasingly vulnerable.
The hidden trade-offs in low-cost networking devices
Consumers often assume that routers are commoditized. If two devices provide similar speeds and coverage, the cheaper option appears rational.
What is invisible in that comparison is the security posture.
Low-cost routers frequently:
- Run outdated Linux kernels or third-party components with known vulnerabilities
- Lack secure boot mechanisms or firmware integrity checks
- Use hardcoded credentials or insecure configuration defaults
- Fail to encrypt management interfaces properly
These trade-offs are not accidental. They are the direct result of cost optimization.
Security is not free. When the price drops, something is removed. In many cases, it is the assurance that the device can withstand real-world adversarial conditions.
Why routers are uniquely dangerous attack surfaces
Routers occupy a uniquely powerful position in any network.
They are:
- Always on
- Directly exposed to the internet
- Responsible for routing all inbound and outbound traffic
- Trusted by every connected device
This combination makes them high-value targets.
This risk is amplified in connected environments where multiple devices share the same network, a problem explored in Smart Home Cybersecurity: 7 Alarming Risks You Must Know.
When a laptop is compromised, the attacker gains access to that device. When a router is compromised, the attacker gains visibility and potential control over everything connected to it.
Research shows that compromised routers can be used to intercept traffic, manipulate DNS responses, and establish persistent access channels that are difficult to detect or remove , as shown in research on compromised routers.
Even more concerning, large-scale studies have found that over 95 percent of residential routers are vulnerable to at least one form of attack, according to large-scale router vulnerability studies, highlighting how widespread the issue has become.
How Low-Cost Devices Become Trojan Horses Inside Your Network
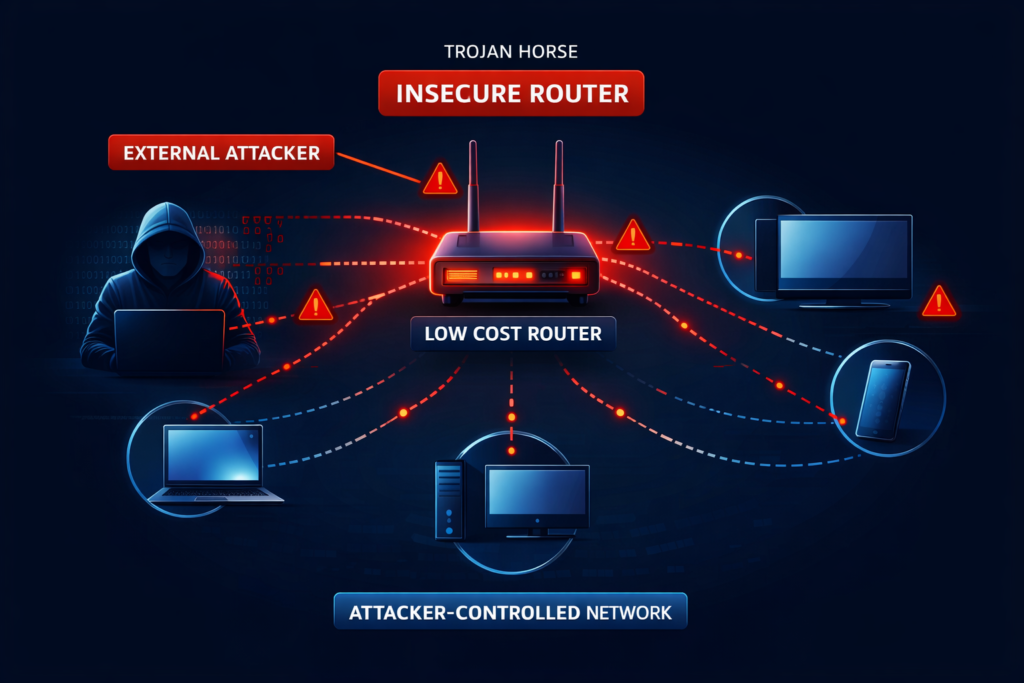
From consumer device to attacker-controlled asset
The transformation of a router into a malicious asset is often simple.
Attackers typically rely on automated scanning tools that continuously probe the internet for exposed devices. These tools look for:
- Default or weak credentials
- Known firmware vulnerabilities
- Open management ports
Once a vulnerable router is identified, exploitation can occur in seconds.
Malware like Mirai was specifically designed to exploit this weakness. It scans for devices using factory credentials and infects them without user interaction, as demonstrated by Mirai botnet behavior.
This is not a targeted attack. It is industrialized exploitation at scale.
Botnet recruitment and remote command execution

After compromise, the router becomes part of a larger controlled network.
Botnets built from routers and IoT devices can:
- Launch distributed denial-of-service attacks
- Relay malicious traffic
- Act as proxy infrastructure for cybercrime
The Mirai botnet demonstrated how powerful this model can be, infecting thousands of devices and enabling attacks that disrupted major online services during the Mirai attacks.
This model has not disappeared. It has evolved.
A 2026 law enforcement operation dismantled a botnet that had infected over 369,000 routers and IoT devices across 163 countries, using them for fraud, ransomware distribution, and proxy services in a large-scale 2026 botnet operation.
Persistence and invisibility
Router compromises are particularly dangerous because they are difficult to detect.
Unlike endpoint malware, router infections:
- Do not appear in antivirus scans
- Persist across device reboots in some cases
- Operate at the network level rather than the application level
Many users never log into their router after initial setup. This creates a blind spot that attackers exploit.
Once inside, they can maintain long-term access, monitor traffic, and pivot to other devices without triggering obvious alerts.
If you are not actively monitoring your network infrastructure, you are operating on trust rather than verification.
Stay ahead of emerging threats, real-world exploits, and practical defenses by subscribing to Quantum Cyber AI.
The Hidden Dangers of Weak Firmware, Shady Supply Chains, and Default Settings
Default credentials and open ports

The most exploited vulnerability in cheap routers is also the simplest: default configuration.
Many devices ship with:
- Default usernames and passwords like “admin/admin”
- Remote management enabled by default
- Open ports exposed to the internet
Attack tools continuously scan for these conditions. Malware like Mirai was explicitly designed to brute-force default credentials at scale, compromising devices within minutes of being connected online through automated Mirai-style attacks.
This is not sophisticated hacking. It is opportunistic automation.
The persistence of this issue highlights a systemic failure in secure-by-default design.
Firmware vulnerabilities and patching failures
Firmware is the core operating system of a router. In low-cost devices, it is often the weakest link.
Common issues include:
- Outdated components with known vulnerabilities
- Lack of cryptographic signing for firmware updates
- No automatic update mechanism
- Delayed or nonexistent security patches
These weaknesses are actively exploited. A single campaign targeting router vulnerabilities leveraged at least 22 known flaws across multiple vendors, demonstrating how attackers reuse and scale exploits across device ecosystems across multiple known router vulnerabilities.
The situation becomes more dangerous when devices reach end-of-life status. Unsupported routers no longer receive patches, yet remain widely deployed.
Recent reporting shows that older models still in circulation contain critical remote code execution vulnerabilities that allow full device takeover in vulnerable router models.
Supply chain risks and geopolitical concerns
Router security is no longer just a technical issue. It is a supply chain and geopolitical concern.
Governments are increasingly scrutinizing networking equipment due to concerns about:
- Hidden backdoors
- Firmware tampering
- Vendor influence or coercion
Recent U.S. policy discussions have identified certain foreign-manufactured routers as potential national security risks due to their role in critical infrastructure and data flows in recent U.S. policy discussions.
This reflects a broader reality.
When you install a router, you are not just buying hardware. You are implicitly trusting:
- The integrity of its firmware
- The security practices of its manufacturer
- The update pipeline that maintains it
In low-cost devices, that trust is often unverified.
How Attackers Use Insecure Routers for Spying, Botnets, and Lateral Movement
Traffic interception and DNS hijacking
A compromised router sits at the most advantageous point in the network. It does not need to break into individual devices because it already controls the pathways between them.
This allows attackers to operate at the traffic level rather than the endpoint level, which is both more efficient and harder to detect.
In practical terms, this enables:
- Interception of unencrypted traffic, including legacy HTTP services and poorly configured applications
- Collection of metadata from encrypted traffic, including domains, timing, and communication patterns
- DNS manipulation, redirecting legitimate domains to attacker-controlled infrastructure
DNS hijacking is particularly effective because it exploits user trust. A user can type a correct URL and still be redirected to a malicious destination without any visible indication.
Even in environments where HTTPS is widely adopted, attackers can still extract meaningful intelligence from traffic patterns and selectively target downgrade or phishing attacks.
This shifts the threat model from device compromise to network-level surveillance and manipulation.
Proxy networks and anonymized cybercrime
Compromised routers are increasingly used as infrastructure rather than endpoints.
Instead of launching attacks directly, adversaries route malicious activity through infected devices, creating distributed proxy networks that obscure attribution.
These networks are used to support:
- Fraud operations that require residential IP legitimacy
- Credential stuffing campaigns designed to evade rate limiting and detection
- Ransomware infrastructure that relies on distributed command and control
The key advantage is plausible legitimacy. Traffic originating from residential routers blends into normal internet activity, making it significantly harder for defenders to distinguish between benign and malicious behavior.
At scale, this creates a layer of operational anonymity that is difficult to dismantle without coordinated law enforcement action.
Lateral movement into connected devices
Once a router is compromised, it becomes a strategic foothold.
Unlike external attackers who must penetrate each device individually, a compromised router allows internal access to the network environment itself.
This enables:
- Scanning of internal IP ranges for vulnerable devices
- Exploitation of unpatched systems within the network
- Credential harvesting through redirected or intercepted traffic
In home environments, this exposes smart devices, personal systems, and network-attached storage.
In hybrid work scenarios, the implications are more severe. A compromised home router can act as a bridge into enterprise environments through:
- VPN connections
- Remote desktop access
- Synced corporate devices
This effectively collapses the boundary between personal and organizational security.
The router is no longer just a device. It becomes a pivot point for broader network compromise.
In practical terms, this mirrors broader smart home exposure patterns outlined in How to Secure Your Smart Home from Hackers: The Ultimate Guide 2025
Warning Signs Your Router May Be Compromised
Network-level anomalies
The earliest indicators of router compromise rarely present as clear security alerts. Instead, they appear as subtle deviations in network behavior that are easy to misattribute to service providers or normal fluctuations.
These include:
- Persistent degradation in network performance without a corresponding increase in legitimate usage
- Irregular bandwidth spikes, particularly during periods of low or no activity
- Increased latency or intermittent connectivity across multiple devices simultaneously
What distinguishes malicious activity from normal variation is consistency and pattern. Botnet-infected routers, for example, generate continuous low-level outbound traffic to command-and-control infrastructure. This traffic may be small in volume but persistent over time.
In contrast, typical consumer usage is bursty and tied to user activity. A network that remains active even when idle should be treated as suspicious.
Configuration changes and unauthorized control
A more definitive indicator of compromise is the presence of unauthorized configuration changes within the router itself.
These may include:
- DNS settings altered to point to unfamiliar or external servers
- New administrative accounts that were not created by the user
- Remote management features enabled without explicit action
- Firewall or port forwarding rules modified unexpectedly
These changes are not cosmetic. They are functional mechanisms attackers use to maintain persistence and control.
DNS manipulation, in particular, is a high-impact technique. By controlling DNS resolution, an attacker can selectively redirect traffic, enabling credential harvesting, phishing, or content injection without requiring endpoint compromise.
If configuration changes reappear after being reset, this may indicate that the underlying firmware has been modified or reinfected.
Behavioral indicators tied to botnet and proxy activity
Compromised routers that are integrated into botnets or proxy networks exhibit distinct behavioral signatures.
These include:
- Continuous outbound connections to geographically distributed or unfamiliar IP addresses
- Repetitive, low-volume traffic patterns consistent with automated command polling
- Participation in high-volume outbound traffic bursts during coordinated attack windows
In proxy-based abuse scenarios, the router may relay third-party traffic that has no relation to the user’s activity. This can result in:
- Unexpected data usage increases
- IP reputation degradation
- Potential service restrictions from providers
One of the most overlooked risks is that users often detect these symptoms only after secondary consequences appear, such as account lockouts or flagged network activity.
Distinguishing false positives from real compromise
Not all anomalies indicate malicious activity. Modern networks generate background traffic from legitimate sources, including:
- Software updates
- Cloud synchronization services
- IoT device communication
The key distinction lies in intent and traceability.
Legitimate traffic can typically be traced to known services or devices. Malicious traffic often:
- Connects to unknown or unrecognized endpoints
- Persists regardless of user behavior
- Resumes after superficial remediation steps
Without visibility tools, this distinction can be difficult to make. However, consistent unexplained behavior should not be dismissed.
When uncertainty is itself a warning sign
A critical but often ignored indicator is lack of visibility.
If you cannot:
- Identify all devices connected to your network
- Verify your router’s configuration integrity
- Confirm that firmware is current and untampered
Then you are operating in a state of assumed trust.
In modern threat environments, that assumption is increasingly invalid.
Uncertainty is not neutral. It is a risk condition.
How to Choose a Safer Router Without Overspending

Security features that actually matter
Router security is not defined by branding or price tier. It is defined by specific architectural and operational controls that determine how the device behaves under real-world attack conditions.
The most critical features are those that reduce both exposure and persistence.
These include:
- Automatic firmware updates that are enabled by default and delivered over secure channels
- Cryptographically signed firmware to ensure that updates have not been tampered with
- Secure boot processes that prevent unauthorized code from executing during startup
- The ability to fully disable remote management and unnecessary services
- Transparent vulnerability disclosure practices from the vendor
These controls are not interchangeable. A router that lacks firmware signing, for example, may still be vulnerable even if it receives updates, because the update mechanism itself can be exploited.
The goal is not feature accumulation, but assurance of integrity across the device lifecycle.
Vendor reputation and update discipline
The long-term security of a router is determined less by its hardware and more by the behavior of its manufacturer after the device is deployed.
Key evaluation criteria include:
- Duration of firmware support relative to product release
- Frequency and timeliness of security updates
- Public documentation of vulnerabilities and remediation actions
- Clear end-of-life policies
For a breakdown of more secure router options with stronger update support, see Best Wi-Fi Mesh Systems for Privacy & Security (2025).
Vendors that treat security as an ongoing responsibility maintain update pipelines that respond to newly discovered threats. Others effectively abandon devices after release, leaving known vulnerabilities unpatched indefinitely.
This creates a predictable pattern. Attackers increasingly target devices that are still widely deployed but no longer supported, because they represent stable, unchanging attack surfaces.
Purchasing decisions should therefore prioritize update discipline over raw specifications.
Avoiding false economies in low-cost devices
The primary risk with cheap routers is not that they fail immediately, but that they degrade into insecurity over time.
A device that is functional but no longer supported becomes progressively more vulnerable as new exploits are developed and published.
This creates a false economy:
- Lower upfront cost
- Increasing long-term exposure
- No viable remediation once support ends
In contrast, a slightly higher investment in a device with a longer support lifecycle reduces cumulative risk across years of use.
The relevant metric is not purchase price, but risk per year of operation.
Building a practical evaluation framework
Rather than relying on marketing claims or surface-level comparisons, router selection should follow a simple evaluation framework:
- Determine whether the device receives automatic, signed firmware updates
- Verify the vendor’s historical track record for patching vulnerabilities
- Confirm that unnecessary services can be disabled and that configuration is transparent
- Identify the expected support lifecycle and end-of-life timeline
- Assess whether the device architecture includes secure boot and integrity checks
If any of these elements are missing, the device should be treated as a higher-risk option regardless of price or performance.
This approach shifts the decision from feature comparison to risk assessment, which is the appropriate lens for network infrastructure.
What to Do Right Now If You Suspect Your Router Is a Security Risk

Immediate containment steps
When router compromise is suspected, speed matters, but so does sequencing. Acting without structure can leave persistence mechanisms intact.
The first objective is containment.
Disconnect the router from the internet to interrupt any active command-and-control communication. This prevents further data exfiltration and stops the device from participating in external activity such as botnet operations.
Once isolated, perform a full factory reset using the hardware reset function rather than a software-based reset. This increases the likelihood of clearing volatile compromises, although it does not guarantee removal of more advanced persistence mechanisms.
After reset:
- Install the latest firmware directly from the manufacturer’s official source
- Change all administrative credentials using unique, non-default values
- Disable remote management and any services not explicitly required
- Reconfigure the network manually rather than restoring from a backup
Restoring previous configurations can reintroduce vulnerabilities or malicious settings.
Verification and validation
After initial remediation, the next step is verification.
A reset device is not inherently a secure device. It must be validated before being trusted again.
This includes:
- Confirming that firmware is up to date and matches the vendor’s latest release
- Reviewing all configuration settings for unexpected changes
- Identifying and validating all connected devices on the network
- Monitoring outbound traffic patterns for abnormal behavior
At this stage, the goal is to determine whether the compromise was superficial or indicative of a deeper issue.
If anomalous behavior resumes after reset and update, this suggests either reinfection or firmware-level compromise.
Network restructuring and risk reduction
Even after remediation, the original conditions that allowed compromise may still exist.
To reduce future exposure:
- Segment IoT and low-trust devices onto a separate network
- Limit administrative access to specific devices where possible
- Implement DNS filtering or upstream security controls
- Regularly review connected devices and network activity
Segmentation is particularly important. It ensures that a single compromised device cannot provide unrestricted access to the entire network.
This shifts the architecture from flat and permissive to segmented and controlled.
Conclusion
Routers are no longer passive infrastructure. They are active participants in the cybersecurity landscape, capable of being weaponized at scale.
Cheap router security risks reflect a deeper problem: the normalization of insecure devices at the foundation of modern connectivity.
As botnets grow, supply chain risks intensify, and attackers continue to exploit weak firmware and default configurations, the role of the router has shifted. It is no longer just a convenience device. It is a critical security boundary.
Treating it as such is no longer optional.
Key Takeaways
- Cheap router security risks are systemic, not isolated
- Routers are high-value targets due to their central network position
- Default credentials and outdated firmware remain primary attack vectors
- Botnets and proxy networks actively exploit insecure devices
- Supply chain trust is now part of the security equation
- Replacing unsupported hardware is often the most effective defense
FAQ
Can a router really spy on you?
Yes. A compromised router can monitor traffic, redirect connections, and observe metadata about your online activity. While encrypted traffic limits visibility, DNS manipulation and traffic routing still enable significant surveillance capabilities.
Are expensive routers always safer?
No. Price alone does not guarantee security. However, higher-quality vendors are more likely to provide ongoing updates, better firmware integrity, and stronger default configurations.
How often should you replace your router?
Typically every 3 to 5 years, or sooner if the device reaches end-of-life and no longer receives security updates.
Is firmware updating enough to stay safe?
Not always. Firmware updates reduce risk, but they cannot fix insecure hardware design, weak default configurations, or supply chain concerns. In some cases, replacement is the only reliable solution.
If you want clear, source-backed insights on emerging cyber threats and practical defenses that actually work, subscribe to Quantum Cyber AI.
